EU digital sovereignty in contract management: what it actually means for European companies
European companies handling regulated information, such as personal health information (PHI), anti-money laundering (AML) data, and complex supplier structures, are entering a new phase of accountability. Digital sovereignty is increasingly an operational requirement influencing how digital infrastructure, applications, and data ecosystems are designed, deployed, and governed.
Driven by EU initiatives such as the Data Act, DORA, NIS2, and the emerging EU Cloud Sovereignty Framework, organizations must ensure that sensitive contract data remains under European legal, technical, and operational control. This shift reflects a broader geopolitical and economic objective: reducing dependency on non-EU digital infrastructure and ensuring that European data is governed by European rules.
As highlighted by the European Commission and policy research bodies, digital sovereignty is about more than data location. It encompasses control over infrastructure, access, governance, and even AI systems. For contract lifecycle management (CLM), this fundamentally changes how companies select vendors, structure contracts, and manage risk.
This article will explore:
- What EU digital sovereignty means in the context of CLM
- The shift from compliance by contract to compliance by architecture
- How to apply sovereignty requirements using key regulatory frameworks
- How EU-based private AI protects sensitive data
- The contract safeguards and vendor criteria for sovereign CLM
- Best practices for future-proofing contract management
- The trade-offs and broader implications of sovereignty requirements
What does EU digital sovereignty mean for contract management?
At its core, EU digital sovereignty means that European organizations retain effective control over their data, infrastructure, and digital dependencies, ensuring they are governed exclusively by EU laws and values.
In contract management, this is critical. CLM platforms routinely process highly sensitive data, such as commercial terms, intellectual property, PHI, and AML-linked information, making them part of an organization’s regulated data perimeter.
The EU’s Cloud Sovereignty Framework, first published in 2025 and now regularly updated, formalizes this through structured requirements. The framework lists eight sovereignty objectives, SOV-1 to SOV-8, that determine a provider’s Sovereignty Effectiveness Assurance Level (SEAL), from SEAL-0 (no sovereignty) to SEAL-4 (true EU sovereignty). These frameworks assess not only where data is stored, but:
- Who controls the infrastructure
- Who can access the data (and from where)
- Which legal jurisdictions apply
- How dependencies (e.g., subcontractors, hyperscalers) are managed
Forrester identifies digital sovereignty as a board-level priority reshaping cloud and infrastructure strategy across industries, driven by rising regulatory scrutiny and geopolitical risk. At the same time, Gartner forecasts sovereign cloud spending will reach $80 billion in 2026, highlighting how sovereignty requirements are moving from policy into large-scale operational investment.
Against this backdrop, the EU’s €180 million sovereign cloud tender does more than set procurement benchmarks, it actively reshapes the market by funding EU-native capacity, defining interoperability standards, and accelerating the shift away from dependence on non-European providers. By putting clear sovereignty criteria into public procurement, the initiative makes policy enforceable and gives both public and private organizations a model to follow.
Compliance by contract vs. compliance by architecture
A key shift for European companies is moving from compliance by contract to compliance by architecture.
- Compliance by contract relies on legal clauses, e.g., data processing agreements, SCCs, or vendor commitments, to promise compliance.
- Compliance by architecture ensures that systems are technically incapable of violating sovereignty requirements.
Why this matters:
- Under regulations like DORA and NIS2, operational resilience and ICT risk must be demonstrable, not just documented.
- The EU Data Act emphasizes control, portability, and switching which requires systems that enable these in practice.
- Standards like ISO 27001 and ISO 27701 reinforce the need for enforceable, auditable controls.
How regulated industries meet sovereignty requirements
For sectors such as banking, insurance, and life sciences, digital sovereignty extends well beyond GDPR. It intersects with multiple regulatory frameworks:
1. Data residency and jurisdiction (EU Data Act)
All contract data must be stored and processed within the EU (SOV-1), ensuring EU law governs access and preventing non-EU claims (SOV-2).
2. Operational control and access (DORA, NIS2)
Critical systems must be operated by EU-based personnel (SOV-3), with access strictly limited to EU jurisdictions and no undisclosed remote access from outside the EU (SOV-4).
3. Supply chain transparency (NIS2)
Organizations must map all ICT dependencies, including subcontractors, to eliminate hidden non-EU control layers (SOV-5) and ensure infrastructure independence (SOV-6).
4. Provider governance and independence
Providers must be EU-headquartered, free from non-EU ownership/control (SOV-7), and aligned with EU priorities like interoperability and resilience (SOV-8).
An IDC Worldwide Digital Sovereignty Survey shows that sovereign cloud adoption in Europe rose sharply to around 40% in 2025, up from roughly 30% in 2023–2024, with a further 31% of organizations planning to adopt it. Early 2026 data suggests this momentum is continuing, as more regulated organizations turn sovereignty requirements into concrete procurement criteria.
This shift is reinforced by a Gartner survey of 241 Western European CIOs conducted in November 2025, which found that 61% plan to increase their reliance on local cloud providers, explicitly for geopolitical reasons, a trend Gartner describes as “geopatriation.”
Why EU-based private AI ecosystems matter
As AI becomes embedded in contract management, through clause extraction, risk analysis, and negotiation support, this introduces new risks:
- Contract data used to train models outside the EU
- AI inference pipelines running on non-EU infrastructure
- Lack of transparency in model governance
EU policy direction increasingly emphasizes sovereign AI ecosystems, where:
- Models are trained on EU-controlled data
- Processing occurs within EU infrastructure
- Outputs remain under EU jurisdiction
For CLM, this means choosing vendors whose AI capabilities are fully contained within a sovereign environment, aligning with the EU AI Act and broader sovereignty objectives.
What contract safeguards support EU digital sovereignty?
General counsel and procurement teams should treat sovereignty as a core legal and operational requirement. Contracts must align with technical reality and enforce architectural guarantees.
| Category | Requirement | Purpose / Outcome |
|---|---|---|
| Data localization and jurisdiction | Mandate exclusive EU storage and processing | Ensures data remains under EU legal control |
| Prohibit transfers outside the EU | Eliminates exposure to non-EU jurisdictions | |
| Establish EU jurisdiction for disputes | Guarantees legal clarity and enforceability within the EU | |
| Audit and transparency rights | Require full disclosure of infrastructure and subcontractors | Provides visibility into the full ICT supply chain |
| Validate sovereignty claims (e.g., SEAL levels or equivalent) | Confirms that providers meet stated sovereignty standards | |
| Enable continuous verification | Ensures ongoing compliance, not just point-in-time assurance | |
| Exit and portability (Data Act, DORA) | Guarantee structured data export | Enables smooth data retrieval and transition |
| Ensure interoperability and migration capability | Supports flexibility and reduces dependency risks | |
| Prevent vendor lock-in | Aligns with regulatory requirements for resilience and switching | |
| AI governance | Restrict model training to EU-controlled datasets | Protects sensitive data from external exposure |
| Prevent data leakage through AI processing | Reduces risk of unintended data transfer or reuse | |
| Ensure compliance with the EU AI Act | Aligns AI use with emerging EU regulatory standards |
These safeguards transform sovereignty from a policy goal into enforceable practice.
Best practices for strategic compliance and future-proofing
To operationalize digital sovereignty in CLM, organizations should take a structured approach:
1. Audit current CLM systems
Assess vendors against sovereignty criteria:
- Data location
- Operational control
- Ownership structure
- Supply chain dependencies
If gaps exist, develop a migration roadmap.
2. Align with regulatory frameworks
Integrate requirements from:
- DORA (ICT risk and resilience)
- NIS2 (cybersecurity and supply chain)
- EU Data Act (portability and control)
- ISO 27001 / 27701 (security and privacy governance)
3. Prioritize sovereign architecture
Ensure that:
- Data never leaves EU jurisdiction
- Access is restricted to EU-based personnel
- Infrastructure is free from non-EU control vectors
4. Select EU-native providers
Prefer vendors that:
- Are EU-owned and operated
- Provide full transparency into their stack
- Can demonstrate true sovereignty, not just “EU region” hosting
Be cautious of hyperscaler-based solutions that retain non-EU governance layers.
5. Segment workloads strategically
- Place critical contract data in sovereign environments
- Use hybrid or multi-cloud only where risk is acceptable
- Continuously monitor dependencies and access paths
Potential drawbacks and balanced perspective
Europe’s push for digital sovereignty is often criticized as protectionist or innovation-limiting. Critics, including policy analysts like the Atlantic Council, warn that strict sovereignty requirements could fragment the digital market, increase costs, and make it harder to access global innovation, particularly from US and Asian hyperscalers.
There’s some truth to this. Tighter control over infrastructure and providers can reduce flexibility and make certain advanced capabilities, especially in AI, more expensive or slower to adopt. The risk of “sovereignty traps” is real in theory: if organizations default to weaker local alternatives purely for compliance optics, they may sacrifice performance and scalability.
But in practice, this critique is frequently overstated, especially in regulated sectors.
For industries like finance and life sciences, the trade-off is not between innovation and sovereignty; it’s between controlled innovation and unmanaged risk. Regulations like DORA, NIS2, and the EU Data Act already require demonstrable control over data, access, and dependencies. In that context, relying on infrastructure that remains exposed to non-EU jurisdiction becomes a risk decision, not a neutral choice.
More importantly, the idea that sovereignty limits innovation assumes that capability only exists outside Europe. That assumption is frankly outdated. EU-driven initiatives, such as the €180 million sovereign cloud tender, are explicitly designed to close capability gaps by funding domestic infrastructure, enforcing interoperability, and accelerating the maturity of EU-native providers.
Yes, sovereignty introduces constraints. But those constraints are increasingly becoming the baseline for operating in regulated environments. The real shift is this: instead of asking how to bolt compliance onto global systems, organizations are starting to choose systems that are sovereign by design.
And in that model, sovereignty is the foundation for building resilient, compliant, and future-proof digital infrastructure.
🔑 Key takeaways
- EU digital sovereignty is becoming a baseline operational requirement, shaping how digital infrastructure, applications, and data ecosystems are designed and governed.
- The shift from compliance by contract to compliance by architecture is critical: regulatory expectations under DORA, NIS2, and the EU Data Act require systems that enforce control by design, not just by legal agreement.
- True sovereignty goes beyond data location. It requires EU control over operations, access, supply chains, and increasingly AI systems.
- Contract safeguards must align with technical realities to be effective.
- Concerns about reduced innovation are often overstated, especially in regulated sectors, where control, auditability, and legal certainty outweigh marginal gains in flexibility or scale.
- Organizations that treat sovereignty as a strategic design principle, rather than a compliance checkbox, will be better positioned to manage risk, avoid lock-in, and future-proof their digital operations.
FAQs
EU digital sovereignty means that organizations retain full control over their data, infrastructure, and digital operations under EU jurisdiction. In practice, this includes EU-based data storage, EU-controlled access, transparent supply chains, and protection from non-EU legal exposure.
GDPR focuses on personal data protection and privacy rights. Digital sovereignty goes further by also addressing who controls the infrastructure, who can access the data, and which legal systems apply, including operational, technical, and supply chain dependencies.
Compliance by architecture means systems are designed so that non-compliant actions are technically impossible, not just contractually restricted. For example, if a system physically prevents data from leaving the EU, it enforces sovereignty more reliably than a contractual promise alone.
Not necessarily. However, companies must ensure that any provider used does not introduce non-EU control, access, or legal exposure. In many regulated cases, this leads to prioritizing EU-native providers or tightly controlled hybrid setups.
It requires that AI systems processing contract data operate within EU-controlled environments. This includes ensuring that training data, model processing, and outputs remain within EU jurisdiction and comply with regulations like the EU AI Act.
Companies should prioritize providers that offer:
- EU-based data storage and processing
- EU-controlled operations and support
- Full transparency into infrastructure and subcontractors
- Strong data portability and exit options
- AI capabilities that operate entirely within the EU
These factors ensure compliance not just in contracts, but in system architecture.
The most effective approach is to design systems with sovereignty in mind from the start. This includes choosing EU-based providers, enforcing data localization, minimizing external dependencies, and ensuring interoperability and portability. Treating sovereignty as a design principle helps organizations stay ahead of evolving regulations.
Compare European CLM leaders
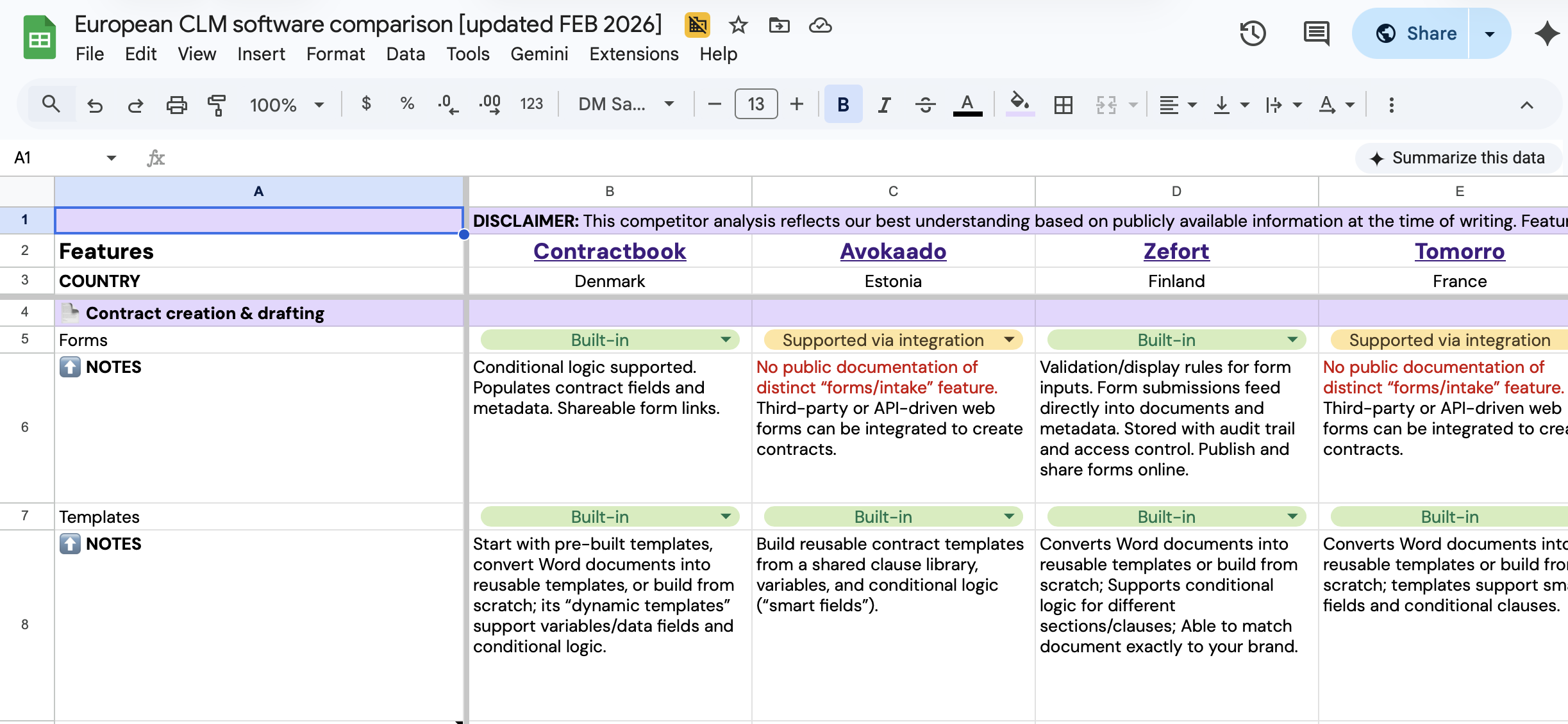
Get a comprehensive breakdown of the top CLM solutions in one spreadsheet.
Compare European CLM leaders
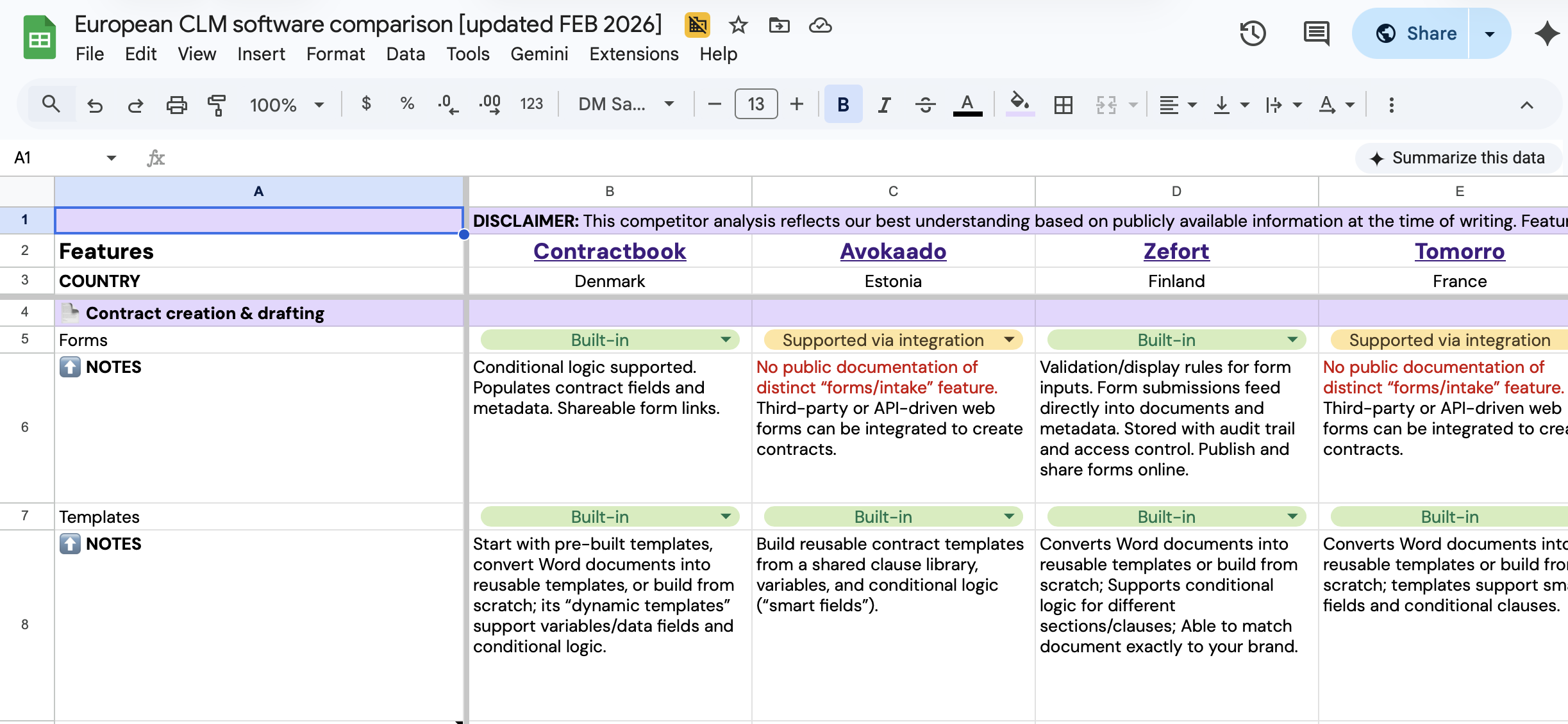
Get a comprehensive breakdown of the top CLM solutions in one spreadsheet.




